Preemptive Cybersecurity: 7 Proven Ways to Stop Threats
Preemptive cybersecurity shifts security teams from waiting for alerts to finding exposure, anticipating attacks, validating controls, and reducing business risk before damage occurs.
Preemptive cybersecurity shifts security teams from waiting for alerts to finding exposure, anticipating attacks, validating controls, and reducing business risk before damage occurs.

In the ever-evolving landscape of cybersecurity, ransomware attacks have emerged as one of the most pervasive and damaging threats. The ability of malicious actors to encrypt critical data and demand a ransom has made ransomware a formidable adversary. Defending against these attacks has become a top priority for organizations across various sectors. This article delves into the intricacies of ransomware defense, covering essential topics such as backup strategies, incident response planning, and the utilization of advanced threat detection technologies.
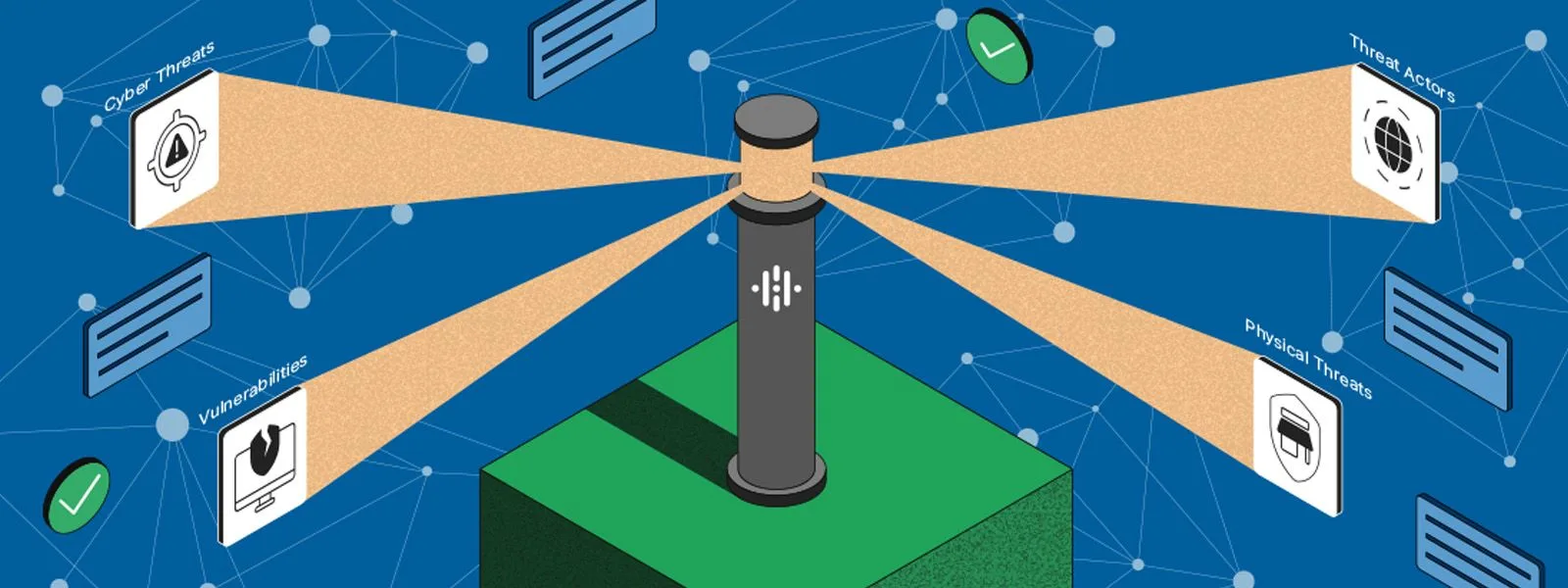
In the realm of cybersecurity, the role of threat intelligence and continuous monitoring has become paramount as organizations face an ever-evolving landscape of cyber threats. By integrating threat intelligence into security operations and embracing continuous monitoring, businesses can enhance their ability to identify, respond to, and mitigate potential security risks. This comprehensive article delves into various aspects of threat intelligence and monitoring, emphasizing best practices, challenges, and the evolving trends shaping the cybersecurity domain.

In the contemporary digital landscape, where the ubiquity of interconnected devices is the norm, ensuring robust endpoint security is paramount. Endpoint security encompasses the protection of devices like computers, smartphones, and other network-connected devices against an array of evolving cyber threats. This comprehensive article delves into the multifaceted realm of endpoint security, exploring its significance, key challenges, essential components, best practices, and emerging trends, with insights drawn from reputable sources in the cybersecurity domain.